TL;DR
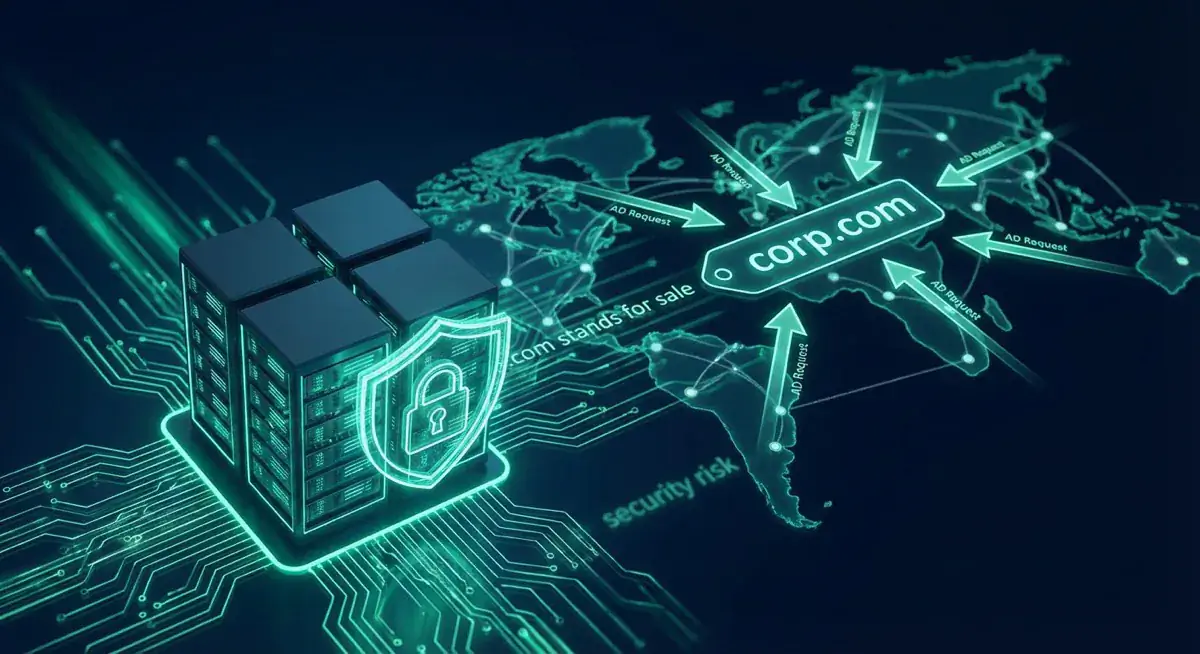
Corp.com, registered in the early 1990s, is being sold for $1.7 million USD, creating a serious security risk. Microsoft's DNS name devolution feature in older Windows versions used 'corp' as an example path, meaning companies that never changed this default may be silently sending sensitive network traffic - including login credentials - to corp.com. A 15-minute experiment confirmed this, receiving 12 million emails and countless login attempts in 30 minutes. The lesson: unmonitored domains, subdomains, and legacy configurations can become serious attack surfaces over time.
Table of Contents (3 sections)
The sale of a domain is actually a very unspectacular event - but it is different with Corp.com. This is because sensitive data is being transferred to this domain. But the owner himself can do little about it. For the domain he wants about 1.7 million USD.
Holder secures early on expensive domains!
It was in the early 90's when Mike O'Connor had the idea to secure some domains. Wise decisions - numerous domains, such as bar.com, were temporarily in his possession. For a large sum of money he separated from them. After almost 26 years he now also wants to part with corp.com. But this could become a problem for the companies that use Microsoft's Active Directory. The blame for this situation lies with the function „DNS name devolution“. Sounds complicated, but makes it easier to use abbreviations. Instead of specifying the complete path, it is sufficient to specify the target drive. Practical in everyday life. Uand this is exactly where the problem lies. Because in old Windows versions Microsoft used the example path "corp". And if this path is not changed, it can happen that sensitive data is transferred to corp.com. Just in the today's time it occurs because in the everyday life constantly, which coworkers want to access internal resources over the Internet.
15-minute experiment with corp.com is aborted!
For 15 minutes the domain was lent for research purposes. In those 15 minutes, according to Jeff Schmidt, "login details rained." The subsequent configuration as an e-mail server confirmed the first snapshot. Within half an hour they received twelve million emails. Among them were a corresponding number of automated requests. But there were also some with sensitive content. As a fun fact: even Microsoft requests were included. If O'Connor had sold the domain to Microsoft for 20,000 USD, the problem would have been largely eliminated. It is not surprising, however, that this deal did not come about. After all, the domain is now for sale for 1.7 million USD. And whoever buys the domain gets the "problem" directly. What happens with the traffic should then be decided by the new owner.
check architecture, placeholders and interfaces in advance!
We look back on a piece of Internet history. The first registration of Corp.com was 26 years ago. Penetration testing and other security investigations were not very common 20 years ago and were rather done as part of quality assurance. Different context, but similar problem are of course QR codes. Once they are printed and static, they point to an Internet address. But if it becomes free and is registered by someone else, you get a problem. For example, QR codes on Heinz ketchup bottles have led to a hardcore porn site. Domains- subdomains and interfaces in general can become a security risk for companies. Monitoring can be done with tools such as RISKREX. A penetration test should always be performed before software is released
Next Step
Our certified security experts will advise you on the topics covered in this article — free and without obligation.
Free · 30 minutes · No obligation
