
TL;DR
Artist Simon Weckert demonstrated a Google Maps hack by loading 99 second-hand smartphones into a handcart and walking through Berlin streets. Because Google Maps interprets many slow-moving devices as traffic congestion, the cart created a virtual traffic jam on otherwise empty roads. The experiment reveals how crowd-sourced navigation data can be manipulated without any traditional cyberattack, raising questions about the reliability of real-time mapping services.
Table of Contents (1 sections)
Most people appreciate the features of integrated navigation tips in smartphones - but how easy are Google Maps Hacks to implement? One artist shows that it is frighteningly easy. And the fascinating consequences of manipulation. For the hack itself, a lot of smartphones are needed. In this case, second hand smartphones will do. 99 of them to be exact. 
It is that easy to clear the streets. 99 second-hand smartphones in a cart (source: simonweckert.com)
Clear the road with 99 second hand smartphones
The success of Google Maps is undisputed. Quite a few people use the app to commute regularly. If the route is congested, it is worth taking a look at the display early in the morning. Until now, there was little doubt that the information displayed was not correct. So far. Simon Weckert has now come up with an idea: The traffic jam display on Google Maps appears when many devices cannot move forward. As can be seen in Simon's handcart, there are some smartphones there that make very slow progress. This is interpreted by Google Maps as a traffic jam. And since there are many devices, it is also a big, red traffic jam. This can also be seen on the screenshots. The whole thing happened in Berlin and shows that this technology can also be manipulated. 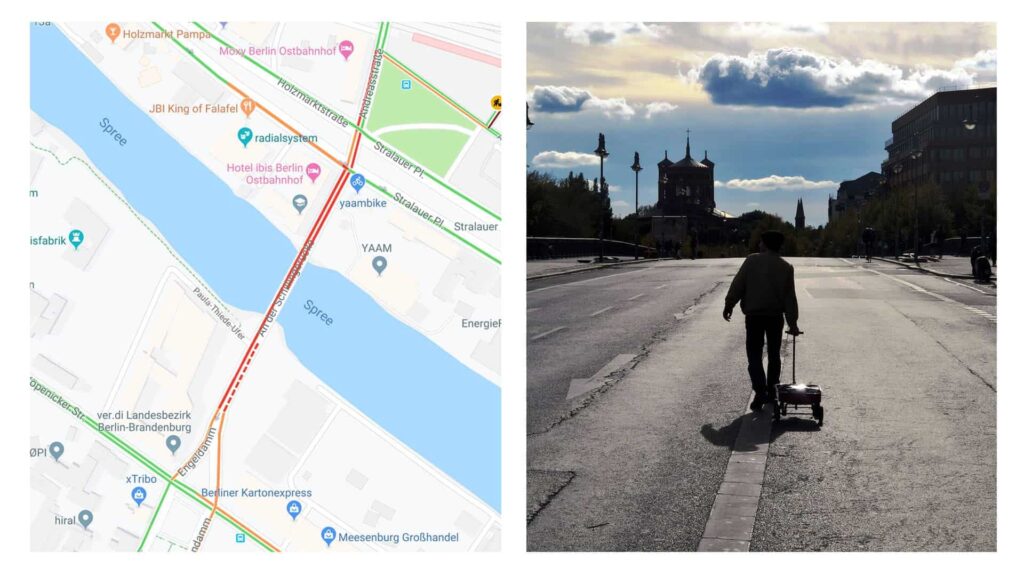
The handcart creates an enormous traffic jam. At least digitally. In reality everything is free. (Quelle: Simonweckert.com)
Google Maps Hacks are possible - but with effort.
Simon's experiment shows that even this technology is far from infallible. The attacks on the reliability of information are simply different from classic cyber attacks. If you can't imagine how it all works live, you can take a look at Simon's video. Empty streets and surprised fellow citizens* can be discovered there. However, the probability that the traffic jam on the A2 is caused by someone with a handcart is quite low. Basically it does not hurt to drive without a navigation system. Maybe you will be happy, like the cars in Berlin, about the one or other free road. https://www.youtube.com/watch?v=k5eL\_al\_m7Q
Next Step
Our certified security experts will advise you on the topics covered in this article — free and without obligation.
Free · 30 minutes · No obligation
